Practical companion artifacts for AEG
This paper defines the AEG model. The public GitHub repository provides the practical reference architecture, diagrams, examples, and supporting materials that accompany it.
The AEG Architecture Model was first published on jacobpallattu.com on December 31, 2025, and subsequently formalized as a canonical technical specification in January 2026.
Abstract
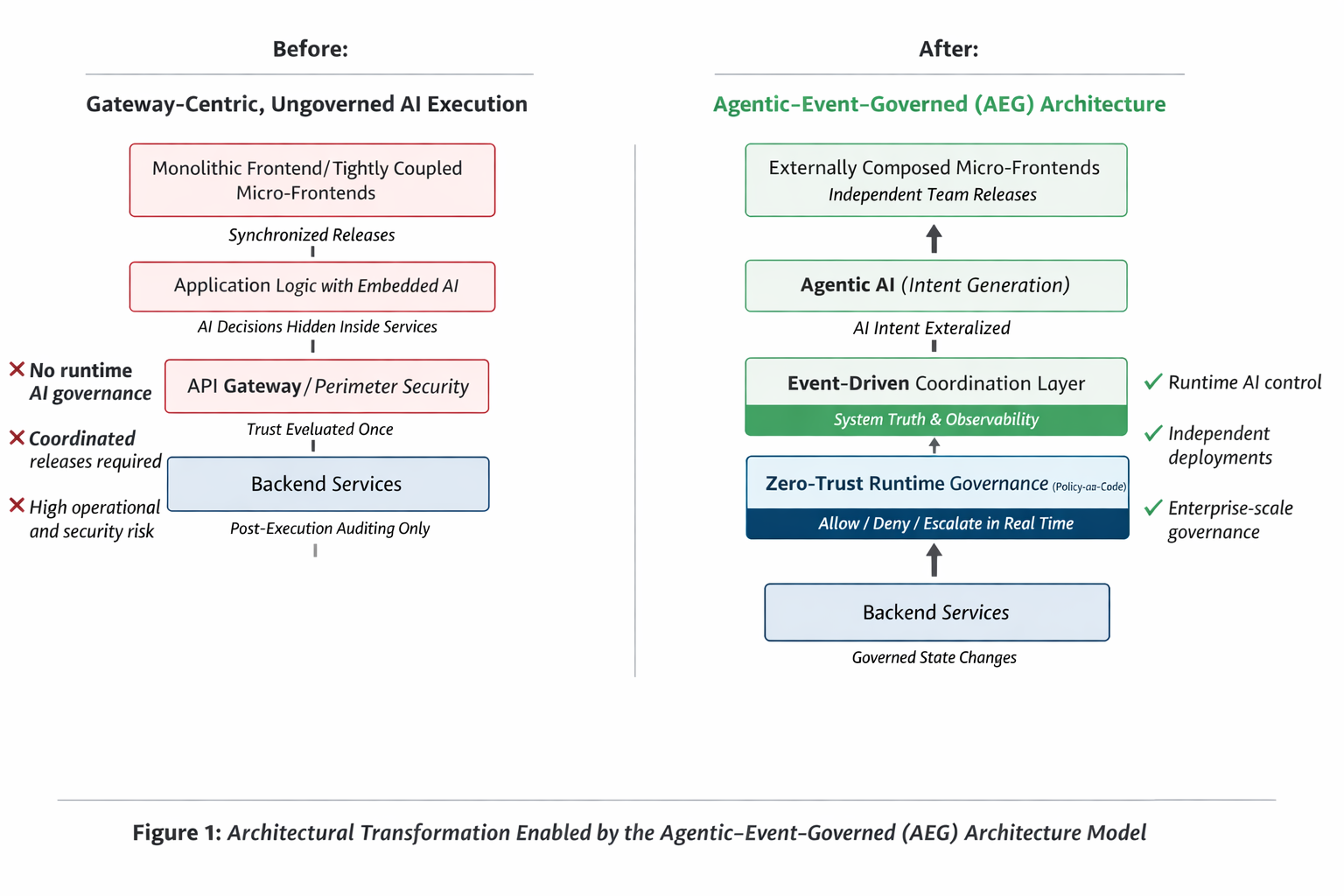
As artificial intelligence systems become increasingly autonomous and agentic, traditional software architecture models struggle to provide adequate control, observability, and security at runtime. Existing approaches often treat AI capabilities, event-driven system design, and zero-trust security as separate concerns, resulting in systems that function under human-initiated workflows but degrade when autonomous behavior, asynchronous execution, and adversarial conditions become dominant.
This paper introduces the Agentic–Event–Governed (AEG) Architecture Model, a unified reference architecture that integrates autonomous AI agents, event-driven coordination, and zero-trust runtime governance as interdependent architectural layers. In the AEG model, agentic components generate intent, event streams serve as the primary coordination and system truth layer, and governance is enforced continuously through policy-as-code mechanisms embedded within system execution rather than at static perimeters or user sessions.
The paper further demonstrates the applicability of the AEG model through a production-grade implementation involving externally composed micro-frontend systems backed by event-driven microservices and AI-generated JSON schemas. In this applied architecture, AI participates across multiple layers, including design-time schema generation, runtime interface personalization, and event-driven system coordination. The resulting system enabled independent team development and release cadences, reduced architectural coupling, and introduced enforceable runtime governance for autonomous behavior.
Together, the AEG Architecture Model and its applied implementation provide a practical foundation for designing AI-native systems that remain intelligent, observable, governable, and resilient under autonomous operation.
1. Introduction
Software architecture is undergoing a structural transition driven by three converging forces: the rise of agentic artificial intelligence, the shift toward event-driven system coordination, and the increasing necessity of zero-trust security models. Each of these forces has been studied independently, yet their combined impact introduces architectural challenges that existing models were not designed to address.
Artificial intelligence is no longer limited to assistive functions or isolated inference services. Modern systems increasingly incorporate agentic AI workloads capable of generating intent, initiating actions, and adapting behavior based on context and feedback. These capabilities fundamentally alter execution dynamics by introducing autonomous actors within software systems. At the same time, distributed architectures are moving away from synchronous, request–response dominance toward asynchronous, event-driven coordination, enabling scalability and decoupling but complicating observability and control. Security architectures, meanwhile, face growing pressure as traditional perimeter- and user-centric trust assumptions erode under autonomous and distributed execution models.
Individually, these trends are manageable. Collectively, they expose a critical gap in architectural reasoning. Systems designed around static control flow, implicit trust boundaries, and post-hoc security enforcement struggle to remain governable once autonomous behavior and asynchronous execution become the norm. As a result, organizations often experience architectures that scale in component count but degrade in predictability, auditability, and control.
Current architectural patterns provide partial solutions. Microservices and micro-frontends improve modularity but often lack a cohesive execution model for system-wide behavior. Event-driven architectures enhance decoupling but are frequently treated as integration mechanisms rather than as foundational coordination and governance layers. Zero-trust principles improve security posture but are commonly applied at system perimeters rather than within runtime execution flows. Agentic AI frameworks enable autonomy but rarely address how autonomous intent should be governed once deployed in production systems.
This fragmentation leads to systems that function adequately under constrained conditions but fail to provide clear answers to fundamental questions as autonomy increases: why a particular action occurred, whether it should have been allowed, and how it can be constrained without reintroducing centralized control or manual intervention.
The Agentic–Event–Governed (AEG) Architecture Model is proposed as a response to this convergence. Rather than layering intelligence, coordination, and security as independent concerns, the AEG model treats them as inseparable components of a unified execution architecture. The model aligns agentic intent generation, event-driven coordination, and zero-trust runtime governance into a coherent framework designed to operate under autonomous, asynchronous, and adversarial conditions.
This paper formalizes the AEG Architecture Model and demonstrates its applicability through a production-grade system that applies AEG principles to externally composed micro-frontends, AI-generated JSON schemas, and event-driven backend services. By grounding the model in a real-world implementation, the paper aims to bridge architectural theory and operational practice, offering a practical foundation for designing AI-native systems that remain observable, governable, and resilient at scale.
2. Related Positioning (and Non-Goals)
AEG is positioned at the intersection of three bodies of practice that are often treated separately: agentic AI frameworks, event-driven architecture, and zero-trust security. Agent frameworks typically focus on planning, tool use, and autonomy, but do not define a runtime governance plane that can intervene as intent turns into action. Event-driven architectures provide scalable coordination and observability, but governance is usually externalized to service boundaries rather than embedded in the event flow. Zero trust improves security posture, yet many implementations remain anchored to perimeter controls and user sessions, which is insufficient when autonomous workloads initiate actions deep inside the system.
AEG does not replace these approaches. It formalizes how they must align when autonomy, asynchrony, and adversarial conditions become default assumptions. The model’s contribution is a unified execution architecture in which intent is explicit, events serve as the primary coordination and truth layer, and policy-as-code enforces trust continuously at runtime.
Non-goals (explicit):
- AEG is not a new agent framework; it is an execution and governance model that existing frameworks can implement.
- AEG is not an eventing technology choice; it is an architectural requirement that events serve as the system’s truth and coordination plane.
- AEG is not perimeter-only zero trust; governance is enforced within runtime flows before state changes.
3. Problem Statement
Building on the architectural shifts outlined in the introduction, this section formalizes the core limitations that emerge when agentic artificial intelligence, event-driven coordination, and zero-trust security are addressed in isolation rather than as a unified system.
Modern software systems are entering a phase where autonomy, asynchrony, and adversarial conditions are no longer edge cases but default operating assumptions. Artificial intelligence is evolving from assistive tooling into agentic workloads capable of generating intent, initiating actions, and adapting behavior with limited or no direct human initiation. At the same time, distributed systems increasingly rely on event-driven coordination rather than synchronous request–response flows. Security architectures, however, continue to rely on assumptions rooted in user-driven interaction, static trust boundaries, and perimeter-based enforcement.
This divergence has created a growing architectural gap: systems that appear modular and scalable at the component level often fail to remain observable, governable, and secure once autonomous behavior and event-driven execution dominate system dynamics. These challenges increasingly affect systems across domains including enterprise platforms, digital products, and AI-driven workflows, regardless of industry or technology stack.
3.1 Limitations of Legacy and Transitional Architectures
Early-generation architectures, particularly monolithic systems, constrained development velocity through tightly coupled codebases, centralized release cycles, and limited parallelism. These constraints made systems brittle under change and difficult to evolve as functional scope and organizational scale increased.
Subsequent adoption of microservices and micro-frontend architectures addressed some modularity concerns but introduced new forms of coupling, particularly in execution coordination, release governance, and cross-team dependency management. In many implementations, micro-frontends remained bound to shared repositories, build pipelines, or synchronized deployment cadences. While code was decomposed, execution and governance were not. Architectural responsibility shifted from monoliths to coordination overhead, without a corresponding execution model capable of reasoning about system behavior holistically.
These limitations became more pronounced as systems incorporated AI capabilities. Intelligence was typically embedded as isolated inference services or decision logic hidden within application code, making autonomous behavior difficult to attribute, observe, or constrain.
3.2 Agentic AI Breaks Traditional Trust Assumptions
Agentic AI systems differ fundamentally from traditional software components. They can generate intent, evaluate context, and trigger actions without explicit user requests. Actions may be initiated by internal reasoning loops, downstream signals, schedules, or interactions with other agents.
This behavior invalidates several assumptions implicit in legacy security and architecture models:
- Actions are primarily user-initiated
- Execution paths are predictable and bounded
- Trust decisions can be anchored to users, sessions, or perimeters
- Authorization can be evaluated once at request entry points
When the system itself becomes an actor, trust can no longer be inferred indirectly. It must be evaluated continuously, at the point where intent turns into action.
3.3 Event-Driven Systems Lack Integrated Governance Models
Event-driven architectures have emerged as a dominant coordination pattern for distributed systems, enabling loose coupling, asynchronous processing, and scalable reaction to change. Events represent facts rather than commands and provide a natural substrate for reasoning, observability, and system evolution.
However, in most architectures, eventing is treated as an integration mechanism rather than a first-class execution and governance plane. While events flow through the system, trust evaluation, authorization, and policy enforcement remain externalized or deferred to service boundaries. This separation limits the ability to reason about causality, intervene in autonomous behavior, or enforce constraints before irreversible state changes occur.
As agentic workloads scale, this gap becomes critical. Systems can observe what happened after the fact but lack the architectural means to govern what is allowed to happen in real time.
3.4 Zero Trust Is Insufficient When Anchored to Perimeters and Users
Zero Trust principles are widely adopted, but many implementations remain implicitly perimeter- or user-centric. Trust is evaluated at API gateways, network boundaries, or authentication layers, assuming that once an internal request is authorized, downstream behavior is implicitly trusted.
In agentic, event-driven systems, this assumption no longer holds. Actions may be triggered deep within the system, long after initial authorization, and may cascade across multiple services and domains. Without runtime governance, systems lack the ability to evaluate intent, context, and risk as behavior unfolds.
Effective zero trust in AI-native systems requires enforcement within the execution flow itself, not only at entry points.
3.5 Absence of a Unified Architectural Model
Across these domains, a common deficiency emerges: the absence of a unified architectural model that explicitly integrates agentic intelligence, event-driven coordination, and zero-trust governance.
Existing architectural patterns describe components, interactions, or security postures in isolation, but do not provide a cohesive execution model for autonomous intent, event-level coordination, and continuous trust evaluation. As a result, organizations build systems that are modular in structure but fragile in behavior, particularly under autonomous operation and scale.
3.6 Introduction of the Agentic–Event–Governed (AEG) Architecture Model
To address these challenges, this paper formalizes the Agentic–Event–Governed (AEG) Architecture Model, a unified reference architecture that treats autonomy, coordination, and governance as inseparable concerns.
In the AEG model:
- Agentic components generate intent and initiate actions
- Event streams serve as the primary coordination and system truth layer
- Zero-trust runtime governance evaluates and enforces policy continuously through policy-as-code mechanisms before actions materialize into state changes
The applicability of the AEG model is demonstrated through a production-grade implementation involving externally composed micro-frontend systems backed by event-driven microservices and AI-generated JSON schemas. This applied architecture enabled independent team development and release cadences, reduced architectural coupling, and introduced enforceable runtime governance across distributed components.
Together, these elements address a class of architectural problems that existing models do not resolve, providing a foundation for building AI-native systems that remain observable, governable, and resilient under autonomous operation.
4. The Agentic–Event–Governed (AEG) Architecture Model
This section formalizes the Agentic–Event–Governed (AEG) Architecture Model as a unified reference architecture for AI-native systems operating under autonomous, asynchronous, and adversarial conditions. The model defines how agentic intelligence, event-driven coordination, and zero-trust runtime governance function together as a single execution framework rather than as layered afterthoughts.
The AEG model is not a technology stack, framework, or implementation pattern. It is an architectural model that describes how intent is generated, how execution is coordinated, and how trust is enforced at runtime in systems where autonomy is a first-class concern.
4.1 Design Goals and Scope
The AEG Architecture Model was designed to address a specific class of systems characterized by:
- Autonomous or semi-autonomous AI agents
- Asynchronous, event-driven execution flows
- Distributed ownership across teams and services
- Continuous security and governance requirements
Within this scope, the model aims to:
- Enable autonomous behavior without sacrificing control
- Preserve loose coupling without losing observability
- Enforce trust continuously at runtime, not only at system boundaries
- Remain technology-agnostic and applicable across domains
The model does not prescribe specific AI models, messaging platforms, or policy engines. Instead, it defines architectural responsibilities and execution semantics that can be realized using different technologies.
4.2 Core Architectural Principle
The foundational principle of the AEG model is that autonomous intent, system coordination, and trust evaluation must be architecturally aligned.
In traditional systems, intent is implicit, coordination is procedural, and trust is enforced at entry points. In AEG, intent is explicit, coordination is event-driven, and trust is evaluated continuously as part of execution.
This alignment is achieved by structuring systems around three interdependent architectural layers:
- Agentic Intelligence Layer
- Event-Driven Coordination Layer
- Zero-Trust Runtime Governance Layer
Each layer has a distinct responsibility, but no layer operates independently.
4.3 Layer 1: Agentic Intelligence Layer
The Agentic Intelligence Layer contains AI agents and reasoning components responsible for intent generation. An agent, in the context of AEG, is not merely a service that invokes an AI model. It is a workload capable of forming objectives, evaluating context, and initiating actions with limited or no direct human initiation.
Key characteristics of agentic components include:
- Intent formation rather than simple request handling
- Context awareness, incorporating signals, state, and constraints
- Action capability, including triggering downstream effects
- Attributable identity, executing as a workload principal
- Governable boundaries, subject to runtime policy enforcement
Crucially, the responsibility of this layer is not execution, but decision-making. Agents emit intent, not side effects. All intent must be externalized in a form that can be observed, evaluated, and governed.
4.4 Layer 2: Event-Driven Coordination Layer
The Event-Driven Coordination Layer serves as the structural backbone of the AEG model. All meaningful decisions, state changes, and outcomes are represented as events flowing through the system.
Within AEG, events function as:
- The primary coordination mechanism between agents and services
- The authoritative system truth layer
- The substrate for observability, causality, and auditability
Events describe what occurred, not what should happen next. This distinction enables loose coupling between decision-making and execution while preserving traceability.
By routing intent and outcomes through events rather than synchronous control flows, the system enables:
- Asynchronous execution and scaling
- Independent evolution of components
- Reconstruction of execution history without relying on service-local logs
The event layer does not embed business logic. It provides the medium through which logic is coordinated and governed.
4.5 Layer 3: Zero-Trust Runtime Governance Layer
The Zero-Trust Runtime Governance Layer enforces trust within execution flows, rather than solely at system boundaries. This layer evaluates whether actions initiated by agents or services are permitted to proceed, based on identity, context, policy, and risk.
In the AEG model, governance operates at the point where intent becomes action.
Key responsibilities of this layer include:
- Continuous identity evaluation of agents and workloads
- Policy enforcement using policy-as-code mechanisms
- Real-time intervention, including allow, deny, delay, transform, or escalate decisions
- Auditability of governance decisions as first-class system events
This approach ensures that autonomous behavior remains controllable without reintroducing centralized orchestration or manual oversight.
4.6 Policy-as-Code as the Governance Bridge
Policy-as-code serves as the execution bridge between intent and action in the AEG model. Policies are expressed independently of application logic and evaluated dynamically as events flow through the system.
Rather than acting as static configuration, policies function as executable architecture. They define:
- Which intents are permitted under specific conditions
- What constraints apply to sensitive operations
- When human intervention is required
By embedding policy evaluation into event flows, governance becomes proactive rather than reactive.
4.7 Execution Semantics and Flow
In an AEG-based system, execution follows a consistent semantic pattern:
- An agent evaluates context and emits intent
- Intent is expressed as an event
- Runtime governance evaluates the event against policy
- Approved actions materialize into execution
- Outcomes generate additional events
This sequence ensures that every autonomous action is observable, attributable, and governable.
4.8 Relationship to Existing Architectural Patterns
The AEG Architecture Model does not replace existing architectural styles but extends them.
- It complements microservices by defining execution semantics
- It strengthens event-driven architectures by introducing governance and intent modeling
- It extends zero-trust principles into runtime behavior
- It provides structure for agentic AI systems operating in production
What differentiates AEG is not any single component, but the explicit alignment of intelligence, coordination, and governance within a unified execution model.
4.9 Summary
The Agentic–Event–Governed (AEG) Architecture Model provides a formal framework for designing AI-native systems that can operate autonomously without sacrificing control, observability, or security. By treating intent, events, and governance as inseparable architectural concerns, the model addresses a class of problems that existing patterns do not resolve in isolation.
The following section demonstrates the applicability of the AEG model through a production-grade system that applies these principles to externally composed micro-frontend architectures with multi-layer AI participation.
5. AEG Applied: Externally Composed Micro-Frontend Systems Using AI-Generated JSON Schemas
This section presents a production-grade application of the Agentic–Event–Governed (AEG) Architecture Model through the design and deployment of an externally composed micro-frontend platform. The applied system demonstrates how AEG principles can be operationalized to address real-world architectural challenges related to frontend scalability, autonomous behavior, governance, and independent team delivery.
The implementation serves as a concrete instantiation of the AEG model, translating its conceptual layers into a working system relied upon by multiple engineering teams. In doing so, it provides empirical grounding for the model’s architectural claims.
5.1 Architectural Context and Pre-Existing Constraints
Prior to the introduction of the AEG-based platform, frontend development evolved through two architectural stages, each revealing distinct limitations.
5.1.1 Legacy Monolithic Frontend
The original frontend architecture consisted of a centralized monolithic codebase. While functionally cohesive, this structure imposed tightly coupled release cycles, limited parallel development, and strong dependency between UI logic and backend services. Even minor changes required coordinated releases across teams, increasing operational risk and slowing delivery.
As system scope and organizational scale increased, these constraints became a persistent bottleneck to both innovation and reliability.
5.1.2 Transitional Micro-Frontend Architecture
To address monolithic limitations, a micro-frontend approach was introduced. However, early implementations remained bound to shared repositories, framework-specific composition mechanisms, and synchronized build pipelines. Although code was decomposed, execution and governance were not.
Teams continued to coordinate deployments, manage shared dependencies, and operate within centralized release constraints. The architecture reduced code size but did not eliminate coupling at the execution level. As AI-driven capabilities were added, intelligent behavior became embedded within individual applications, making system-level reasoning and governance increasingly difficult.
5.2 AEG-Based Design Objectives
The applied architecture was intentionally designed to align with the AEG model and address the observed limitations.
The primary objectives were to:
- Enable independent development and release of frontend components
- Decouple UI composition from build-time and framework dependencies
- Introduce AI as a first-class architectural participant rather than an isolated service
- Establish event-driven coordination as the primary execution backbone
- Enforce zero-trust governance at runtime, within execution flows
These objectives directly map to the agentic, event-driven, and governed layers of the AEG model.
5.3 External Micro-Frontend Composition Model
At the core of the applied system is an externally composed micro-frontend model. Instead of assembling user interfaces at build time, micro-frontends are dynamically loaded, composed, and governed at runtime.
Each micro-frontend:
- Is developed, tested, and deployed independently
- Exposes its capabilities and structure through JSON-based schemas
- Interacts with backend services through event-driven mechanisms
- Operates without compile-time dependency on other micro-frontends
Runtime composition logic determines which micro-frontends are loaded, how they are arranged, and under what conditions they are permitted to execute. This eliminated synchronized release requirements and reduced cross-team coupling while preserving coherent user experiences.
5.4 Multi-Layer AI Participation in the Applied Architecture
A distinguishing characteristic of the applied system is the use of AI across multiple architectural layers, rather than as a single inference capability. Intelligence participates in design-time generation, runtime personalization, and event-driven coordination.
5.4.1 Design-Time AI: Mockups and Wireframes to JSON Schemas
AI models were used to translate design artifacts, such as mockups and wireframes, into structured JSON schema representations. These schemas defined UI layout, components, constraints, and interaction patterns independent of frontend frameworks.
This approach:
- Reduced manual translation between design and implementation
- Standardized UI contracts across teams
- Enabled schema-driven generation and validation of micro-frontends
By positioning AI as a design agent, intelligence was shifted upstream, improving consistency while preserving implementation flexibility.
5.4.2 Runtime AI: Context-Aware UI Personalization
At runtime, AI was applied to personalize user interfaces based on contextual signals, behavioral data, and system state. JSON schemas acted as the contract layer, allowing personalization logic to modify structure and content without direct coupling to frontend codebases.
This enabled dynamic UI adaptation while maintaining governance and auditability. Personalization decisions were expressed as intent and routed through event flows, ensuring traceability and policy enforcement.
5.4.3 Event-Driven AI: Intelligent Coordination and Adaptation
AI-driven decisions were also integrated into the event-driven coordination layer. Events emitted from user interactions, backend services, and system signals triggered adaptive behavior across micro-frontends and microservices.
Routing decisions through events, rather than synchronous calls, preserved loose coupling while enabling intelligent coordination. Events became the authoritative record of system behavior, supporting observability, causality analysis, and continuous learning.
5.5 Event-Driven Backend Alignment
Each micro-frontend was backed by autonomous microservices aligned with the same event-driven execution model. Frontend and backend components communicated through events rather than direct request chains, ensuring consistency across system layers.
Event streams coordinated behavior, captured execution history, and enabled asynchronous scaling. This alignment allowed frontend and backend teams to evolve independently while maintaining coherent system behavior.
5.6 Zero-Trust Runtime Governance
Governance was enforced at runtime through policy-as-code mechanisms embedded within event flows. Rather than relying solely on perimeter controls or static authorization checks, trust decisions were evaluated continuously as intent propagated through the system.
Policies governed:
- Which micro-frontends could be composed under specific conditions
- What actions AI-generated intent was permitted to initiate
- How sensitive operations were gated, delayed, or escalated
This enabled real-time intervention before irreversible state changes occurred, ensuring that autonomous behavior remained observable, controllable, and auditable.
5.7 Organizational Impact
The applied AEG-based architecture produced sustained organizational impact:
- Teams independently developed and released micro-frontends on their own cadence
- Coordination overhead and architectural coupling were significantly reduced
- AI-driven capabilities were introduced without compromising governance or security
- The platform became a shared foundation relied upon by multiple teams
The system transitioned frontend delivery from a coordination-heavy process to an autonomous yet governable architecture aligned with AI-native requirements.
5.8 Alignment with the AEG Architecture Model
This applied system represents a direct instantiation of the AEG Architecture Model:
- Agentic layer: AI-driven intent generation for schema creation, personalization, and coordination
- Event layer: Event streams as the primary coordination and system truth layer
- Governed layer: Zero-trust runtime policy enforcement within execution flows
By aligning these layers, the system demonstrates how AEG can be applied to resolve architectural challenges that existing models do not adequately address in isolation.
The following section outlines an evaluation plan and metrics to assess AEG-based systems in production.
6. Evaluation Plan and Metrics
This section defines how AEG-based systems should be evaluated in production. The intent is to quantify three properties that become critical under agentic, event-driven execution: governability (ability to constrain autonomous intent), observability (ability to reconstruct causality), and delivery autonomy (independent evolution across teams) without weakening security.
6.1 Governance Effectiveness and Risk Mitigation
The Zero-Trust Runtime Governance Layer is evaluated using:
- Intent coverage: percentage of high-risk intents that are policy-evaluated before execution
- Enforcement outcomes: percentage of intents allowed, denied, delayed, transformed, or escalated
- Decision latency: p50/p95/p99 time to reach a governance decision (policy evaluation + routing)
- Blast-radius containment: percentage of blocked intents that would have triggered irreversible state changes or cross-domain effects
These metrics demonstrate whether governance is proactive (pre-state-change) rather than retrospective.
6.2 Observability, Causality, and Detection
Event-driven coordination is evaluated using:
- MTTD for anomalous autonomous behavior: time from anomaly to detection signal
- Causality reconstruction time: time to reconstruct “why this happened” using event lineage rather than service-local logs
- Trace completeness: presence of correlation IDs, parent/child event links, actor identity, policy decision events, and outcome events
- Forensic sufficiency: ability to replay or reconstruct a decision sequence from the event stream within a defined retention window
6.3 Delivery Autonomy and Organizational Efficiency
External composition and schema-driven contracts are evaluated using:
- Deployment independence: number of components deployed without cross-team coordination
- Release cadence: deployment frequency per team before vs. after adoption
- Coordination overhead: effort spent on shared release planning, integration testing, and dependency alignment
- Coupling incidents: incidents attributable to shared UI build pipelines, shared repositories, or synchronized releases
6.4 Adoption and Reuse at Scale
To evaluate whether AEG functions as a reusable architectural standard:
- Onboarding time: time to onboard a new micro-frontend or agentic workload into governance
- Reuse ratio: percentage of new workloads that reuse the same event/governance primitives without bespoke integration logic
- Standardization indicators: number of teams referencing AEG as a design baseline in architecture reviews
This evaluation framing is intended to be technology-agnostic and applicable across organizations.
7. Conclusion and Future Work
This paper introduced the Agentic–Event–Governed (AEG) Architecture Model, a unified reference architecture designed to address the structural challenges that emerge as software systems become increasingly autonomous, event-driven, and security-sensitive. By aligning agentic intelligence, event-driven coordination, and zero-trust runtime governance into a single execution model, AEG provides a coherent framework for designing AI-native systems that remain observable, governable, and resilient under autonomous operation.
Through a production-grade applied system, the paper demonstrated how AEG principles can be operationalized in practice. The externally composed micro-frontend architecture, supported by AI-generated JSON schemas, event-driven backend services, and policy-as-code governance, illustrated how autonomous behavior and independent team delivery can be achieved without sacrificing architectural control. The paper defines an evaluation plan and metrics to assess AEG-based systems in production.
The primary contribution of the AEG Architecture Model lies not in a single technology or implementation detail, but in the explicit alignment of intent generation, execution coordination, and trust enforcement. Existing architectural patterns address these concerns in isolation; AEG formalizes their interdependence and provides a repeatable execution model for systems operating under autonomy and scale.
Future work will focus on extending the AEG model in several directions. These include formalizing intent taxonomies for agentic workloads, expanding governance semantics for cross-domain and multi-organization environments, and exploring automated policy generation and validation techniques. Additional applied case studies across different domains may further validate the model’s generality and adaptability.
As agentic AI systems continue to proliferate, the need for architectures that balance autonomy with control will only increase. The Agentic–Event–Governed Architecture Model offers a foundational step toward that balance, providing a practical and extensible framework for the next generation of AI-native systems.